第十一周作业
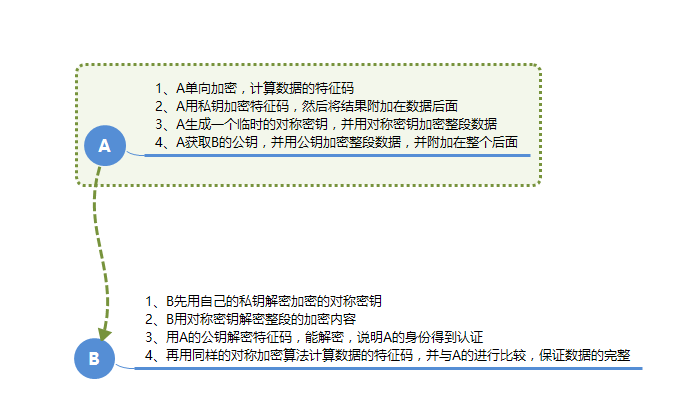
1、详细描述一次加密通讯的过程,结合图示最佳
第一阶段:ClientHello:
支持的协议版本,比如tls 1.2;
客户端生成一个随机数,稍后用户生成“会话密钥”
支持的加密算法,比如AES、3DES、RSA;
支持的压缩算法;
第二阶段:ServerHello
确认使用的加密通信协议版本,比如tls 1.2;
服务器端生成一个随机数,稍后用于生成“会话密钥”
确认使用的加密方法;
服务器证书;
第三阶段:
验正服务器证书,在确认无误后取出其公钥;(发证机构、证书完整性、证书持有者、证书有效期、吊销列表)
发送以下信息给服务器端:
一个随机数;
编码变更通知,表示随后的信息都将用双方商定的加密方法和密钥发送;
客户端握手结束通知;
第四阶段:
收到客户端发来的第三个随机数pre-master-key后,计算生成本次会话所有到的“会话密钥”;
向客户端发送如下信息:
编码变更通知,表示随后的信息都将用双方商定的加密方法和密钥发送;
服务端握手结束通知;2、描述创建私有CA的过程,以及为客户端发来的证书请求进行颁发证书
首先配置CA服务器
1)生成私钥
~]# (umask 077; openssl genrsa -out /etc/pki/CA/private/cakey.pem 4096)
2)生成自签证书
~]# openssl req -new -x509 -key /etc/pki/CA/private/cakey.pem -out /etc/pki/CA/cacert.pem -days 3655
3)创建所需的目录及文件
~]# mkdir -pv /etc/pki/CA/{certs,crl,newcerts}
~]# touch /etc/pki/CA/{serial,index.txt}
~]# echo 01 > /etc/pki/CA/serial
客户端
(1) 用到证书的主机生成私钥;
~]# mkdir /etc/httpd/ssl
~]# cd /etc/httpd/ssl
~]# (umask 077; openssl genrsa -out /etc/httpd/ssl/httpd.key 2048)
(2) 生成证书签署请求
~]# openssl req -new -key /etc/httpd/ssl/httpd.key -out /etc/httpd/ssl/httpd.csr -days 365
(3) 将请求通过可靠方式发送给CA主机;
scp /etc/httpd/ssl/httpd.csr root@CAIPADRESS:/tmp/httpd.csr
CA签署证书并发放证书给请求者
#openssl ca -in /tmp/httpd.csr -out /etc/pki/CA/certs/httpd.crt -days 365
scp /tmp/httpd.csr root@HTTPIPADRESS:/etc/httpd/ssl/httpd.crt3、描述DNS查询过程以及DNS服务器类别
 详情可参见http://blog.chinaunix.net/uid-28216282-id-3757849.html这篇博客,写的很详细
详情可参见http://blog.chinaunix.net/uid-28216282-id-3757849.html这篇博客,写的很详细4、搭建一套DNS服务器,负责解析magedu.com域名(自行设定主机名及IP)
1)能够对一些主机名进行正向解析和逆向解析
#yum -y install bind*
#[root@localhost ~]# vim /etc/named.conf
listen-on port 53 { any; };
dnssec-enable no;
dnssec-validation no;
修改配置文件
vim /etc/named.rfc1912.zones
zone "shoushangdezhu.com" IN {
type master;
file "shoushangdezhu.com.zone";
allow-transfer { slaves; };
};
zone "68.168.192.in-addr.arpa" IN {
type master;
file "192.168.68.134.zone";
};
配置正向,反向zone文件
]# vim /var/named/shoushangdezhu.com.zone
$TTL 3600
$ORIGIN shoushangdezhu.com.
@ IN SOA ns1.shoushangdezhu.com. 18717961178.163.com. (
20170931
1H
10M
3D
1D )
IN NS ns2
IN NS ns3
IN NS ns1.shoushangdezhu.com.
IN MX 10 MX1
ns1 IN A 192.168.68.134
MX1 IN A 192.168.68.150
www IN A 192.168.68.134
web IN CNAME www
bbs IN A 192.168.68.151
ns2 IN A 192.168.68.130
pop3 IN A 192.168.68.135
ppp IN A 192.168.68.156
ns3 IN A 192.168.68.141
ns1.ops IN A 192.168.68.139
]# vim /var/named/192.168.68.134.zone
$TTL 3600
$ORIGIN 68.168.192.in-addr.arpa.
@ IN SOA ns1.shoushangdezhu.com. 18717961178.163.com. (
201709235
1H
10M
3D
12H )
IN NS ns1.shoushangdezhu.com.
IN NS ns2.shoushangdezhu.com.
IN NS ns3.shoushangdezhu.com.
134 IN PTR ns1.shoushangdezhu.com.
134 IN PTR www.shoushangdezhu.com.
151 IN PTR bbs.shoushangdezhu.com.
150 IN PTR pop3.shoushangdezhu.com.
130 IN PTR ns2shoushangdezhu.com.
155 IN PTR bb3.shoushangdezhu.com.
141 IN PTR ns3.shoushangdezhu.com.
添加文件权限
[root@localhost ~]# chgrp named /var/named/shoushangdezhu.cmo.zone
[root@localhost ~]# chmod o= /var/named/ shoushangdezhu.cmo.zone
[root@localhost ~]# chgrp named /var/named/192.168.134.zone
[root@localhost ~]# chmod o= /var/named/192.168.134.zone
检查语法
[root@localhost ~]# named-checkconf
[root@localhost~]#named-checkzone "shoushangdehzu.com" /var/named/magedu.com.zone
[root@localhost ~]# named-checkzone "134.68.168.192.in-addr.arpa" /var/named/192.168.68.134.zone
测试
[root@localhost named]# dig -x 192.168.68.134 @192.168.68.134
; <<>> DiG 9.9.4-RedHat-9.9.4-51.el7 <<>> -x 192.168.68.134 @192.168.68.134
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 17798
;; flags: qr aa rd ra; QUERY: 1, ANSWER: 2, AUTHORITY: 3, ADDITIONAL: 4
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 4096
;; QUESTION SECTION:
;134.68.168.192.in-addr.arpa. IN PTR
;; ANSWER SECTION:
134.68.168.192.in-addr.arpa. 3600 IN PTR ns1.shoushangdezhu.com.
134.68.168.192.in-addr.arpa. 3600 IN PTR www.shoushangdezhu.com.
;; AUTHORITY SECTION:
68.168.192.in-addr.arpa. 3600 IN NS ns2.shoushangdezhu.com.
68.168.192.in-addr.arpa. 3600 IN NS ns3.shoushangdezhu.com.
68.168.192.in-addr.arpa. 3600 IN NS ns1.shoushangdezhu.com.
;; ADDITIONAL SECTION:
ns1.shoushangdezhu.com. 3600 IN A 192.168.68.134
ns2.shoushangdezhu.com. 3600 IN A 192.168.68.130
ns3.shoushangdezhu.com. 3600 IN A 192.168.68.141
;; Query time: 1 msec
;; SERVER: 192.168.68.134#53(192.168.68.134)
;; WHEN: Sun Oct 29 12:52:42 CST 2017
;; MSG SIZE rcvd: 208
[root@localhost named]# dig -t A www.shoushangdezhu.com @192.168.68.134
; <<>> DiG 9.9.4-RedHat-9.9.4-51.el7 <<>> -t A www.shoushangdezhu.com @192.168.68.134
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 7856
;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 3, ADDITIONAL: 4
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 4096
;; QUESTION SECTION:
;www.shoushangdezhu.com. IN A
;; ANSWER SECTION:
www.shoushangdezhu.com. 3600 IN A 192.168.68.134
;; AUTHORITY SECTION:
shoushangdezhu.com. 3600 IN NS ns2.shoushangdezhu.com.
shoushangdezhu.com. 3600 IN NS ns1.shoushangdezhu.com.
shoushangdezhu.com. 3600 IN NS ns3.shoushangdezhu.com.
;; ADDITIONAL SECTION:
ns2.shoushangdezhu.com. 3600 IN A 192.168.68.130
ns3.shoushangdezhu.com. 3600 IN A 192.168.68.141
ns1.shoushangdezhu.com. 3600 IN A 192.168.68.134
;; Query time: 0 msec
;; SERVER: 192.168.68.134#53(192.168.68.134)
;; WHEN: Sun Oct 29 12:53:30 CST 2017
;; MSG SIZE rcvd: 169
2)对子域cdn.magedu.com进行子域授权,子域负责解析对应子域中的主机名
3)为了保证DNS服务系统的高可用性,请设计一套方案,并写出详细的实施过程本文来自投稿,不代表Linux运维部落立场,如若转载,请注明出处:http://www.178linux.com/88118